Vulnerability Report - June 2025
Introduction
This vulnerability report has been generated using data aggregated on Vulnerability-Lookup, with contributions from the platform’s community.
It highlights the most frequently mentioned vulnerability for June 2025, based on sightings collected from various sources, including MISP, Exploit-DB, Bluesky, Mastodon, GitHub Gists, The Shadowserver Foundation, Nuclei, and more. For further details, please visit this page.
The final section focuses on exploitations observed through The Shadowserver Foundation’s honeypot network.
The Month at a Glance
The June 2025 report highlights a mix of long-standing and newly identified high-risk vulnerabilities. Notably, Citrix discloses a critical NetScaler ADC/Gateway flaw (CVE-2025-5777), dubbed “CitrixBleed 2,” which can expose session tokens and bypass multi-factor authentication — echoing last year’s infamous CitrixBleed. Other urgent issues include a PayU India WordPress plugin vulnerability (CVE-2025-31022) that allows full account takeover across thousands of sites, and a Python “tarfile” library bug (CVE-2025-4517) that enables attackers to write files outside intended directories. Among the most sighted vulnerabilities are multiple Microsoft Windows 10 and Google Chrome flaws, as well as several Citrix ADC bugs, many rated “High” or “Critical.” Common web weaknesses like cross-site scripting and SQL injection (CWE-79, CWE-89) remain widespread, highlighting the ongoing need for strong patching hygiene. Some older vulnerabilities — such as the 2015 D-Link DIR-645 flaw and known Confluence or Cisco RCE bugs — also continue to see active exploitation. Organizations should prioritize remediation of these critical and actively targeted vulnerabilities, while reinforcing application security against injection and XSS attacks.
Top 10 vulnerabilities of the Month
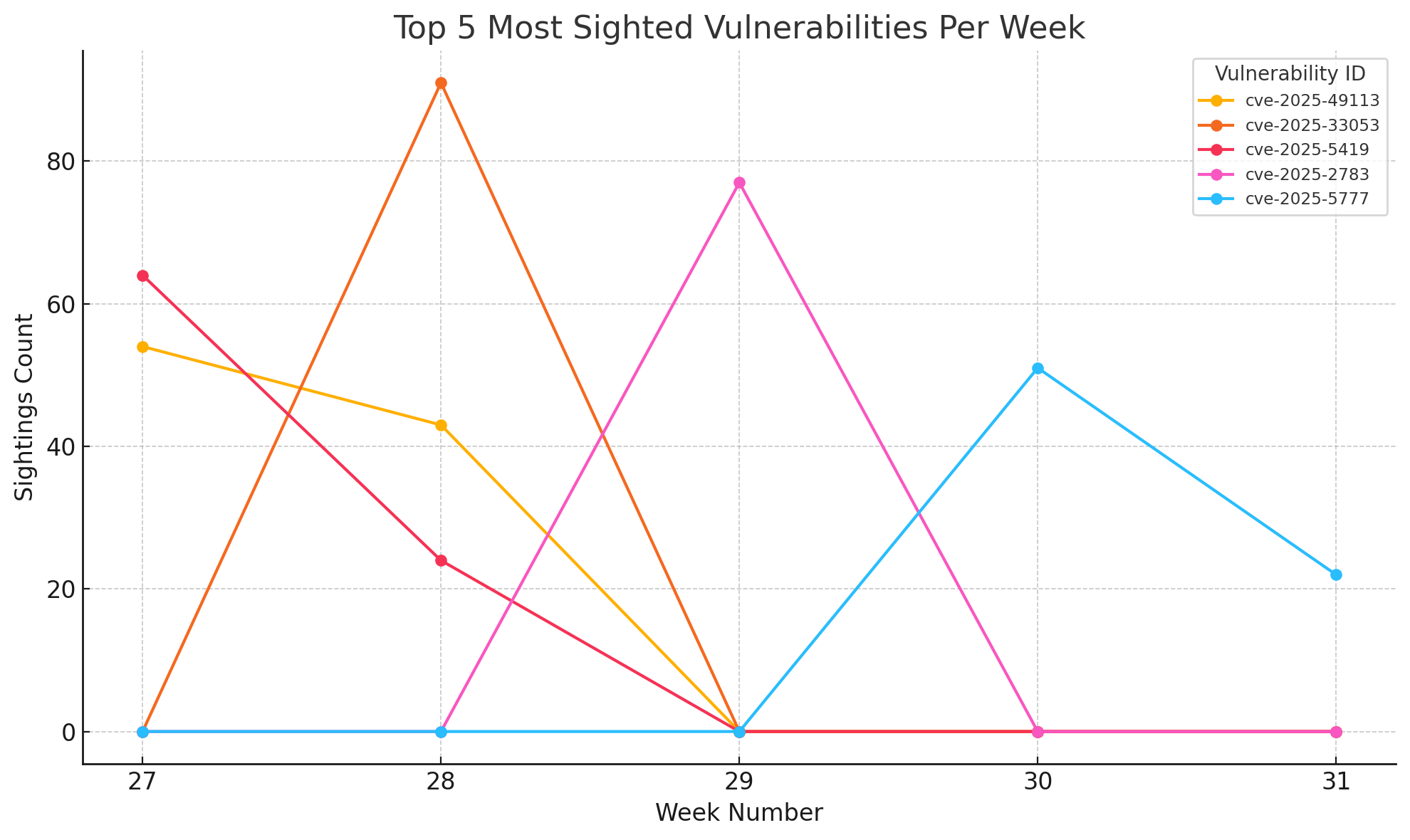
Evolution of sightings per week
Top 10 Weaknesses of the Month
| CWE | Number of vulnerabilities |
|---|---|
| CWE-79 | 659 |
| CWE-89 | 411 |
| CWE-74 | 342 |
| CWE-119 | 190 |
| CWE-862 | 157 |
| CWE-352 | 157 |
| CWE-120 | 105 |
| CWE-94 | 94 |
| CWE-22 | 86 |
| CWE-98 | 74 |
Insights from Contributors
CitrixBleed 2
Citrix patched a critical vulnerability in its NetScaler ADC and NetScaler Gateway products that is already being compared to the infamous CitrixBleed flaw exploited by ransomware gangs and other cyber scum, although there haven’t been any reports of active exploitation. Yet.
Security analyst Kevin Beaumont dubbed the vulnerability “CitrixBleed 2.” As The Register’s readers likely remember, that earlier flaw (CVE-2023-4966) allowed attackers to access a device’s memory, find session tokens, and then use those to impersonate an authenticated user while bypassing multi-factor authentication — which is also possible with this new bug.
GCVE-1-2025-0002: Cl0p Ransomware Data Exfiltration Vulnerable to RCE Attacks A newly identified security vulnerability in the Cl0p ransomware group’s data exfiltration utility has exposed a critical remote code execution (RCE) flaw that security researchers and rival threat actors could potentially exploit.
The vulnerability, designated as GCVE-1-2025-0002, was published on July 1, 2025, and carries a high severity rating of 8.9 on the CVSS:4.0 scale.
- CVE-2010-2568 MS10-046 Windows
- CVE-2010-2729 MS10-061 Windows
- CVE-2008-4250 MS08-067 Windows
- CVE-2010-2772 Not Available Siemens SIMATIC WinCC
CVE-2025-31022: More details about PayU wordpress extension
“This can be abused by a malicious actor to perform action which normally should only be able to be executed by higher privileged users. These actions might allow the malicious actor to gain admin access to the website.”
CVE-2025-4517: Additional information
RISK : Multiple vulnerabilities affect the standard TarFile library for CPython. Currently, there is no indication that the vulnerability is actively exploited, but because it is a zero-day with a substantial install base, attackers can exploit it at any moment. An attacker could exploit flaws to bypass safety checks when extracting compressed files, allowing them to write files outside intended directories, create malicious links, or tamper with system files even when protections are supposedly enabled. Successful exploitation could lead to unauthorised access, data corruption, or malware installation, especially if your systems or third-party tools handle untrusted file uploads or archives RECOMMENDED ACTION: Patch Source: ccb.be
Continuous Exploitation
- CVE-2025-32433 - erlang / otp
- CVE-2015-2051 - D-Link / DIR-645
- CVE-2022-26134 - Atlassian / Confluence Data Center
- CVE-2019-1653 - Cisco / Cisco Small Business RV Series Router Firmware
Thank you
Thank you to all the contributors and our diverse sources!
If you want to contribute to the next report, you can create your account.
Feedback and Support
If you have suggestions, please feel free to open a ticket on our GitHub repository. Your feedback is invaluable to us!
https://github.com/vulnerability-lookup/vulnerability-lookup/issues/