Vulnerability Report - February 2026
Introduction
This vulnerability report has been generated using data aggregated on Vulnerability-Lookup, with contributions from the platform’s community.
It highlights the most frequently mentioned vulnerability for February 2026, based on sightings collected from various sources, including MISP, Exploit-DB, Bluesky, Mastodon, GitHub Gists, The Shadowserver Foundation, Nuclei, SPLOITUS, Metasploit, and more. For further details, please visit this page.
The Month at a Glance
February 2026 was led by CVE-2026-1731, a Critical-severity issue affecting BeyondTrust Remote Support (RS) and Privileged Remote Access (PRA), with 158 sightings. It was followed closely by CVE-2026-2441 in Google Chrome with 143 sightings.
Microsoft-related vulnerabilities were also prominent in the top 10, including CVE-2026-20841 (Windows Notepad) and CVE-2026-21509 (Microsoft 365 Apps for Enterprise). Other heavily sighted entries spanned enterprise recovery and networking products such as Dell RecoverPoint for Virtual Machines (CVE-2026-22769) and Cisco Catalyst SD-WAN Manager (CVE-2026-20127), as well as platform and tooling ecosystems like Apple macOS (CVE-2026-20700), Ivanti Endpoint Manager Mobile (CVE-2026-1281), and n8n (CVE-2026-25049).
February continued to be an active month for known exploited vulnerabilities. The CISA Known Exploited Vulnerabilities catalog added 28 new entries during the month. Notable additions include:
- CVE-2026-1731: BeyondTrust Remote Support (RS) & Privileged Remote Access (PRA)
- CVE-2026-2441: Google Chrome
- CVE-2026-20127: Cisco Catalyst SD-WAN Manager
- CVE-2026-22769: Dell RecoverPoint for Virtual Machines
- CVE-2025-49113: Roundcube Webmail
- CVE-2020-7796: synacor zimbra_collaboration_suite
The CIRCL Known Exploited Vulnerabilities catalog added three entries (CVE-2026-25108, CVE-2026-1340, and CVE-2026-1281), while the ENISA KEV catalog had no new entries in February.
The Ghost CVE Report highlights eight vulnerability identifiers that were observed in sightings despite limited or missing public records. The most frequently sighted were CVE-2023-42344 (5 occurrences) and CVE-2026-1584 (4 occurrences), followed by CVE-2026-23456 (3 occurrences).
Contributor insights this month covered Cisco Catalyst SD-WAN vulnerabilities, an IceWarp command-injection RCE, analysis of CVEs affecting the Svelte ecosystem, TP-Link VIGI IP camera issues, and reporting on UAC-0001 (APT28) activity leveraging CVE-2026-21509.
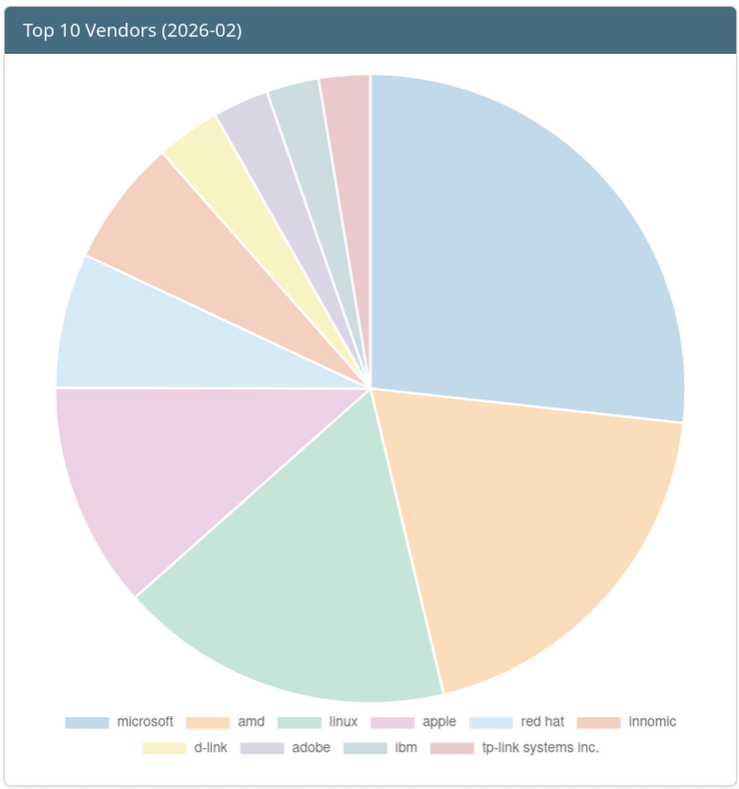
Top 10 Vendors of the Month
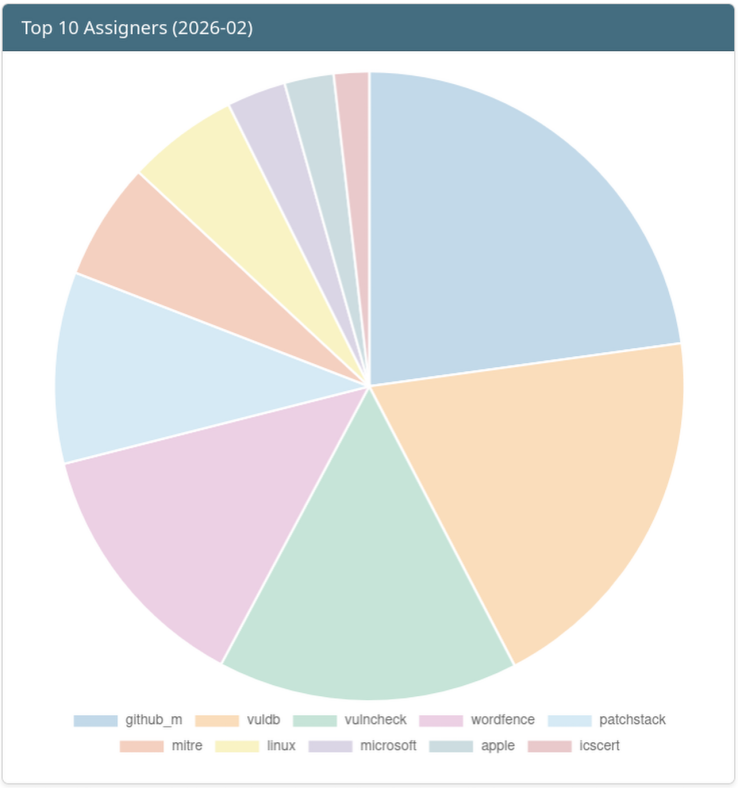
Top 10 Assigners of the Month
Top 10 vulnerabilities of the Month
| Vulnerability | Sighting Count | Vendor | Product | VLAI Severity |
|---|---|---|---|---|
| CVE-2026-1731 | 158 | BeyondTrust | Remote Support(RS) & Privileged Remote Access(PRA) | Critical (confidence: 0.9914) |
| CVE-2026-2441 | 143 | Chrome | High (confidence: 0.9908) | |
| CVE-2026-20841 | 131 | Microsoft | Windows Notepad | High (confidence: 0.9833) |
| CVE-2026-21509 | 113 | Microsoft | Microsoft 365 Apps for Enterprise | High (confidence: 0.9687) |
| CVE-2026-22769 | 91 | Dell | RecoverPoint for Virtual Machines | Critical (confidence: 0.9356) |
| CVE-2026-20127 | 76 | Cisco | Cisco Catalyst SD-WAN Manager | Critical (confidence: 0.9411) |
| CVE-2026-20700 | 69 | Apple | macOS | High (confidence: 0.9705) |
| CVE-2026-1281 | 69 | Ivanti | Endpoint Manager Mobile | Critical (confidence: 0.9791) |
| CVE-2026-25253 | 55 | OpenClaw | OpenClaw | High (confidence: 0.7975) |
| CVE-2026-25049 | 54 | n8n-io | n8n | Critical (confidence: 0.617) |
Known Exploited Vulnerabilities
New entries have been added to major Known Exploited Vulnerabilities catalogs.
CISA
More KEV entries from the CISA Catalog.
CIRCL
| CVE ID | Date Added | Vendor | Product | VLAI Severity |
|---|---|---|---|---|
| CVE-2026-25108 | 2026-02-26 | Soliton Systems K.K. | FileZen | High (confidence: 0.8244) |
| CVE-2026-1340 | 2026-02-03 | Ivanti | Endpoint Manager Mobile | Critical (confidence: 0.9791) |
| CVE-2026-1281 | 2026-02-03 | Ivanti | Endpoint Manager Mobile | Critical (confidence: 0.9791) |
More KEV entries from the CIRCL Catalog.
ENISA
No new entry in February.
More KEV entries from the ENISA Catalog.
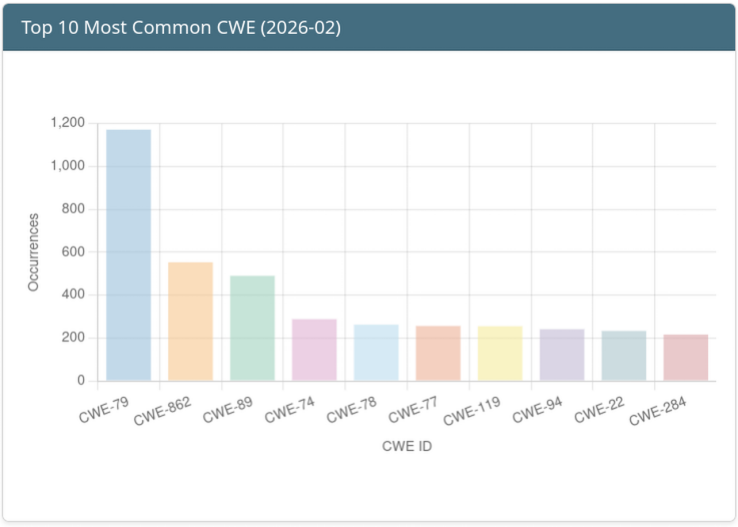
Top 10 Weaknesses of the Month
Click the image for more information.
Ghost CVE Report
A ghost CVE is a vulnerability identifier that’s already popped up in the wild but is still listed as RESERVED or NOT_FOUND in official registries like NVD or MITRE.
Sightings detected between 2026-02-01 and 2026-02-28 that are associated with vulnerabilities without public records.
| Vulnerability ID | Occurrences | Comment |
|---|---|---|
| CVE-2023-42344 | 5 | OpenCMS Unauthenticated XXE Vulnerability |
| CVE-2026-1584 | 4 | libgnutls: Fix NULL pointer dereference in PSK binder verification |
| CVE-2026-23456 | 3 | YoSmart YoLink Smart Hub |
| CVE-2025-15576 | 2 | FreeBSD 14.3 and 13.5 (Jail chroot escape via fd exchange with a different jail) |
| CVE-2026-3038 | 2 | All supported versions of FreeBSD (Local DoS and possible privilege escalation via routing sockets) |
| CVE-2025-13050 | 2 | Multiple vulnerabilities in Centreon products |
| CVE-2025-12523 | 2 | Multiple vulnerabilities in Centreon products |
| CVE-2025-71210 | 2 | Multiple vulnerabilities in Trend Micro products (KA-0022458) |
Insights from Contributors
- Cisco Catalyst SD-WAN Vulnerabilities
- IceWarp14 X-File-Operation Command Injection Remote Code Execution Vulnerability
- MajorDoMo Revisited: What I Missed in 2023
- CVEs affecting the Svelte ecosystem
- TP-Link Systems Inc. VIGI Series IP Camera
- UAC-0001 (APT28) carries out cyberattacks against Ukraine and EU countries using the exploit CVE-2026-21509
Thank you
Thank you to all the contributors and our diverse sources!
If you want to contribute to the next report, you can create your account.
Feedback and Support
If you have suggestions, please feel free to open a ticket on our GitHub repository. Your feedback is invaluable to us!
https://github.com/vulnerability-lookup/vulnerability-lookup/issues/
Funding

The main objective of Federated European Team for Threat Analysis (FETTA) is improvement of Cyber Threat Intelligence (CTI) products available to the public and private sector in Poland, Luxembourg, and the European Union as a whole.
Developing actionable CTI products (reports, indicators, etc) is a complex task and requires an in-depth understanding of the threat landscape and the ability to analyse and interpret large amounts of data. Many SOCs and CSIRTs build their capabilities in this area independently, leading to a fragmented approach and duplication of work.
The Computer Incident Response Center Luxembourg (CIRCL) is a government-driven initiative designed to provide a systematic response facility to computer security threats and incidents. The organization brings to the table its extensive experience in cybersecurity incident management, threat intelligence, and proactive response strategies. With a strong background in developing innovative open source cybersecurity tools and solutions, CIRCL’s contribution to the FETTA project is instrumental in achieving enhanced collaboration and intelligence sharing across Europe.