Vulnerability-Lookup 4.2.0 released
It is our honour to announce the release of Vulnerability-Lookup 4.2.0!
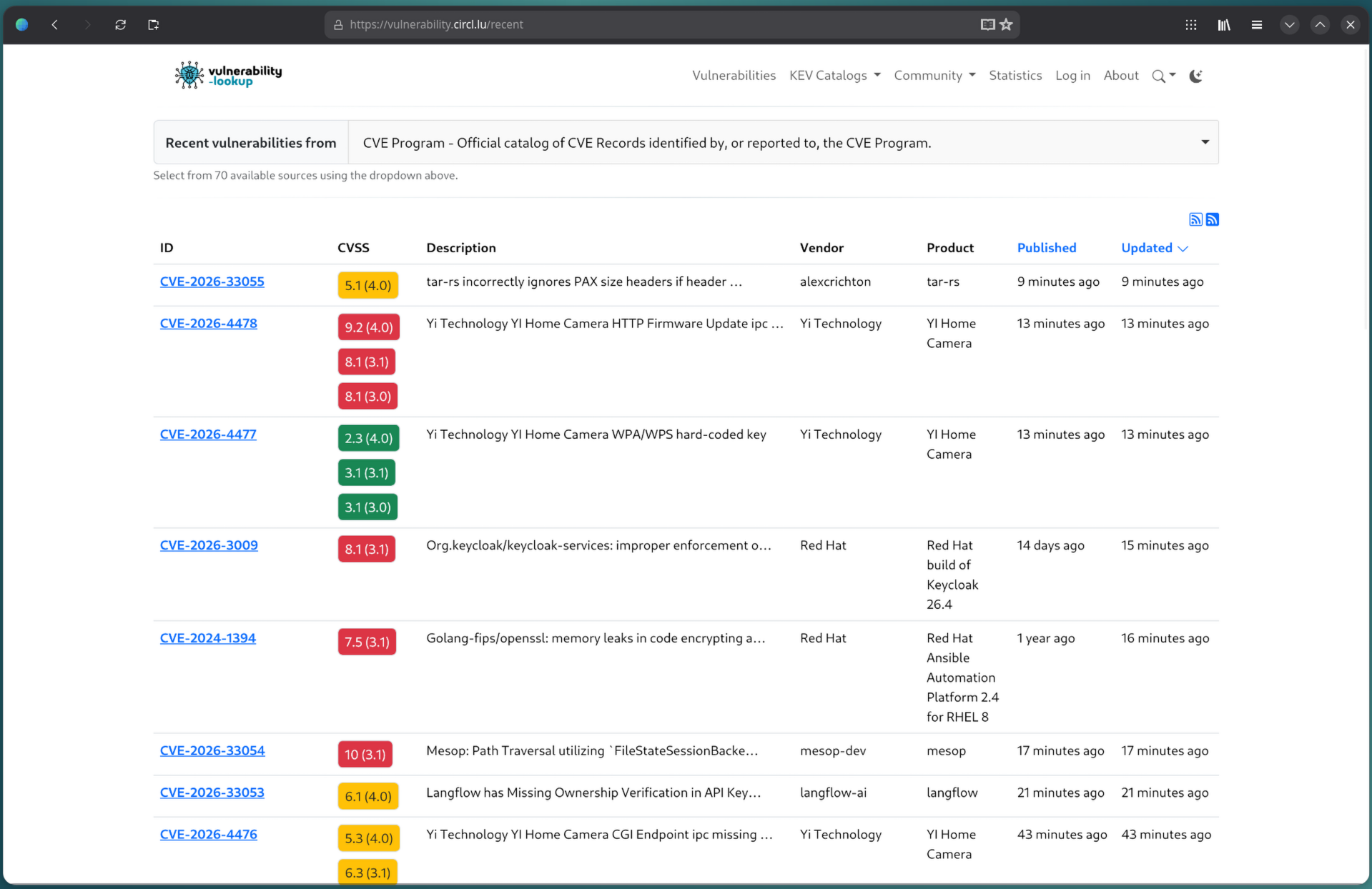
This version brings a large number of new CSAF-based vulnerability advisory sources, improvements to the web interface, and several bug fixes.
What’s New
New CSAF-based sources
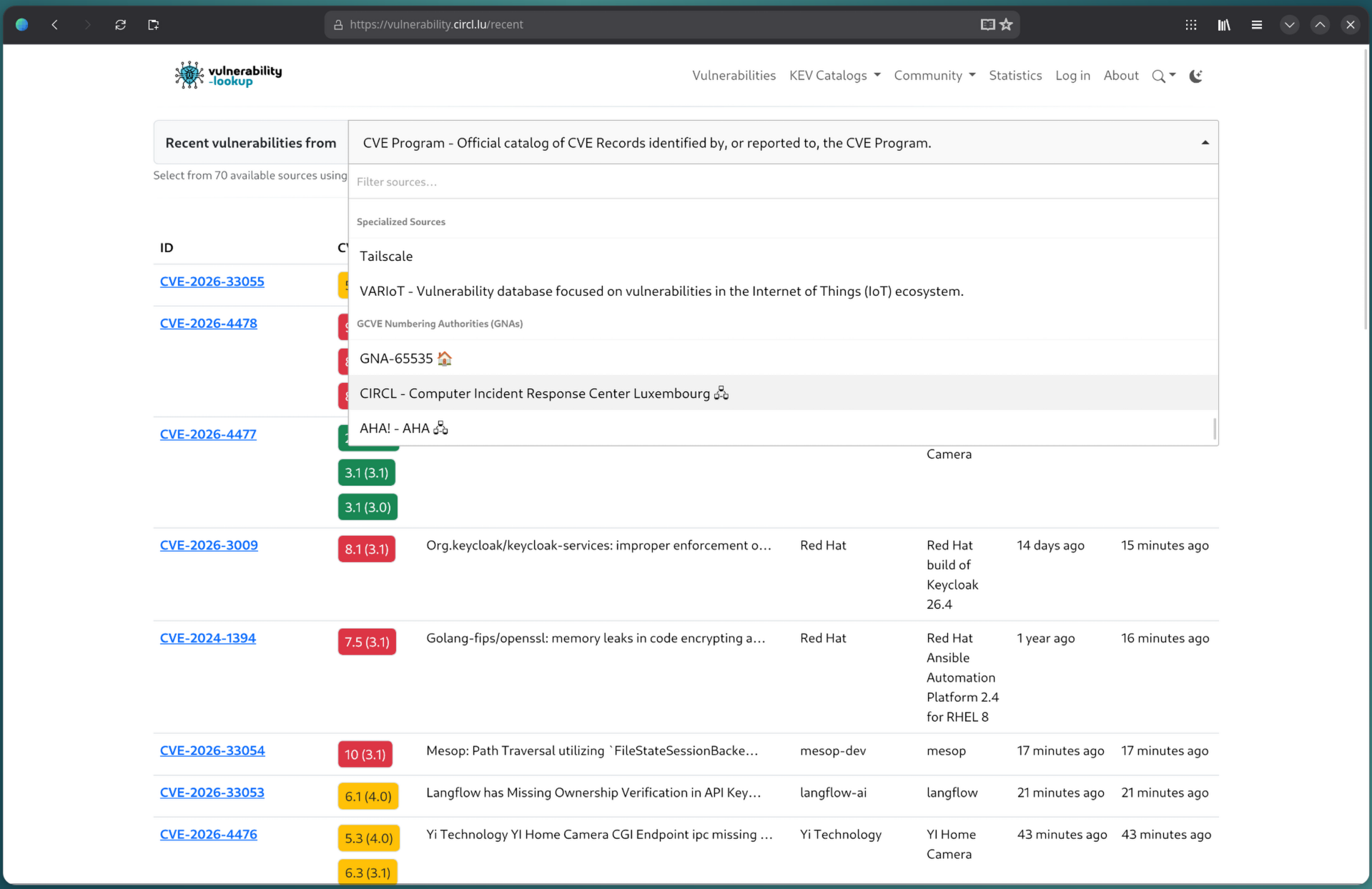
As the number of GNA keeps growing and the interest around the GCVE-EU initiative increases, these UI improvements and filtering capabilities are becoming essential to efficiently explore the various available sources.
Below is the list of CSAF-based sources available by default. You can enable or disable each feeder via the
config/modules.cfg configuration file. The display in the web interface is also configurable through the
config/website.py configuration file.
- ABB
- ads-tec Industrial IT GmbH
- AUMA Riester GmbH & Co. KG
- Beckhoff Automation GmbH & Co. KG
- Bender GmbH & Co. KG
- Carlo Gavazzi Automation
- CERT-Bund
- CERT@VDE
- CISA
- Cisco
- CODESYS GmbH
- Endress+Hauser AG
- Festo SE & Co. KG
- Frauscher Sensortechnik GmbH
- Helmholz GmbH & Co. KG
- HIMA Paul Hildebrandt GmbH
- ifm electronic GmbH
- Janitza electronics GmbH
- Lenze SE
- MB connect line GmbH
- Mettler-Toledo GmbH
- Microsoft
- Miele & Cie KG
- Murrelektronik GmbH
- NCSC-NL
- Nozomi Networks
- Open-Xchange
- OpenSuse
- Pepperl+Fuchs SE
- Phoenix Contact GmbH & Co. KG
- Pilz GmbH & Co. KG
- Red Hat
- Sauter AG
- Schneider Electric
- Sick
- Siemens
- SMA Solar Technology AG
- Suse
- SWARCO TRAFFIC SYSTEMS GmbH
- Trumpf SE + Co. KG
- VARTA Storage GmbH
- WAGO GmbH & Co. KG
- Weidmueller Interface GmbH & Co. KG
- Welotec GmbH
- Wiesemann & Theis GmbH
Improvements
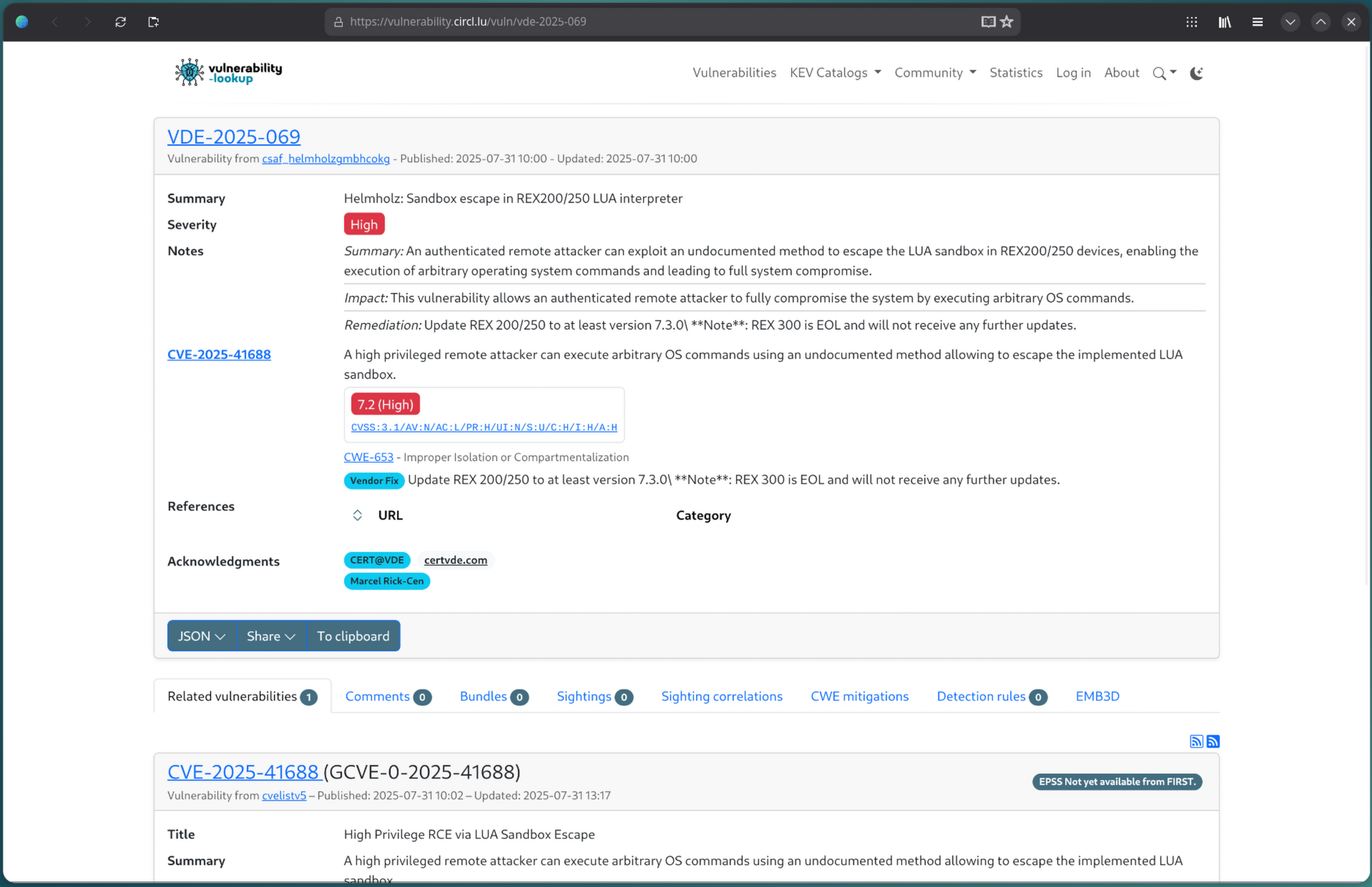
Enriched CSAF view
The generic CSAF view now includes severity, vulnerabilities, references, and acknowledgments.
d528da8Enriched OSV view
Added severity and references to the generic OSV view.
65de73eDate published in CVE records
If known, thedatePublicfield of CVE records is now displayed.
861a082Boost recent sightings enabled by default
The boost recent sightings switch is now checked by default.
4eed4c4New source argument for the full-text indexer
Added asourceargument to the indexer for more targeted indexing.
d4e6e1fLess verbose indexing
Reduced the verbosity of the full-text search indexing process.
a563dffConfiguration improvements
Reorganized the defaultSOURCES_TO_SHOWconfig variable and updated the samplewebsite.pyconfiguration with examples for the new configuration options.
f699400, 6e8fb6cDocumentation updates
Various improvements to the documentation, including GCVE publication as a GNA and Known Exploited Vulnerabilities Catalogs.
58a4d83, 143f5f5, 1f6d6d3, 52c774fUpdated Python dependencies
6e30dc2
Fixes
- Fixed incorrect vulnerability ID passed in various Jinja macros. cf1b209
- Fixed the default product option so the form correctly re-submits its value when changing sort/order controls. 7373f8f
- Suppressed spurious config warnings for disabled features. c82e911
- Fixed a variable shadowing issue in
parse_vuln_payload()where the localsourcevariable was overriding the function parameter. cb03721
Changelog
📂 For the full list of changes, check the GitHub release:
https://github.com/vulnerability-lookup/vulnerability-lookup/releases/tag/v4.2.0
🙏 Thank you to all contributors and testers!
Special thanks to Raphaël Vinot for adding the new sources.
Feedback and Support
If you encounter any issues or have suggestions, feel free to open a ticket on our GitHub repository:
https://github.com/vulnerability-lookup/vulnerability-lookup/issues/
Your feedback is always appreciated!
Follow Us on Fediverse/Mastodon
You can follow us on Mastodon and get real-time information about security advisories:
https://social.circl.lu/@vulnerability_lookup/